Section 3
Infrastructuring autonomy: protocol level solutions for countering isolation
MahsaNet: building grassrooted resilience
MahsaNet is a grassroots, globally distributed engineering effort born out of Iran’s escalating censorship regime and sharpened by wartime shutdown conditions. What began as an Android-only circumvention app evolved, under intense political and technical pressure, into a full-stack resilience ecosystem designed to survive deep packet inspection, IP blocking, infrastructure takedowns, and even coordinated disinformation campaigns targeting the tool itself.
At its core, MahsaNet is structured around a dynamic relationship between MahsaServer and client applications such as MahsaNG VPN. MahsaServer aggregates a massive collection of donated VPN configurations and distributes them intelligently based on real-time conditions . One of its key innovations is a “protocol availability radar,” which continuously assesses which protocols are currently viable under Iran’s filtering regime. This is critical in an environment where censorship tactics shift rapidly—through SNI filtering, TLS fingerprinting, active probing, or wholesale IP blocking. Instead of relying on static endpoints, the system pushes working configurations dynamically to clients, enabling over 3.5 million successful connections per day .
On the client side, MahsaNG is a heavily customized fork of v2rayNG and xray-core. By building on these flexible proxy frameworks and integrating custom components such as “knocker-core,” MahsaNet can rapidly adapt transport layers and obfuscation strategies. The architecture is designed for agility: configurations rotate, protocols shift, and endpoints evolve as soon as filtering patterns are detected. With more than 1.5 million active users, the system functions less like a traditional VPN service and more like a distributed, adaptive tunneling network.
The year 2025 marked a decisive escalation. Funding cuts destabilized the broader circumvention ecosystem, other tools became ineffective, Iran’s filtering apparatus grew stricter, and Cloudflare actions disrupted proxy infrastructures. During the Iran–Israel conflict, the regime imposed a full internet shutdown while simultaneously launching disinformation and malware campaigns against MahsaNet itself. In response, the team overhauled backend infrastructure, released multiple new versions of its clients, and expanded into cross-platform support, including iOS. This period transformed MahsaNet from a single application into an integrated resilience platform.
A central component of this expansion is the SegmentVPN SDK, an open-source, cross-platform VPN framework built with Flutter and designed around a multi-core architecture supporting engines such as knocker-core and Outline. Its modular structure allows other developers to integrate circumvention capabilities directly into their own applications. This reduces monoculture risk: rather than one easily fingerprinted app, circumvention becomes diffusely embedded across multiple tools. For users on the ground, this diversification makes blanket blocking more difficult. If one signature is detected and filtered, alternative implementations remain viable.
Complementing this client layer is CompassVPN, a scalable, self-hosted VPN server agent with built-in monitoring, automated management, and horizontal scaling features. By enabling activists, diaspora communities, or civil society actors to deploy and manage their own infrastructure, CompassVPN reduces reliance on large commercial cloud providers that may withdraw support under political pressure. Automated firewall configuration, ingress management, and monitoring dashboards allow rapid redeployment when IP ranges are blocked. In shutdown conditions, the capacity to spin up new nodes quickly can determine whether connectivity resumes in hours or remains suppressed for days.
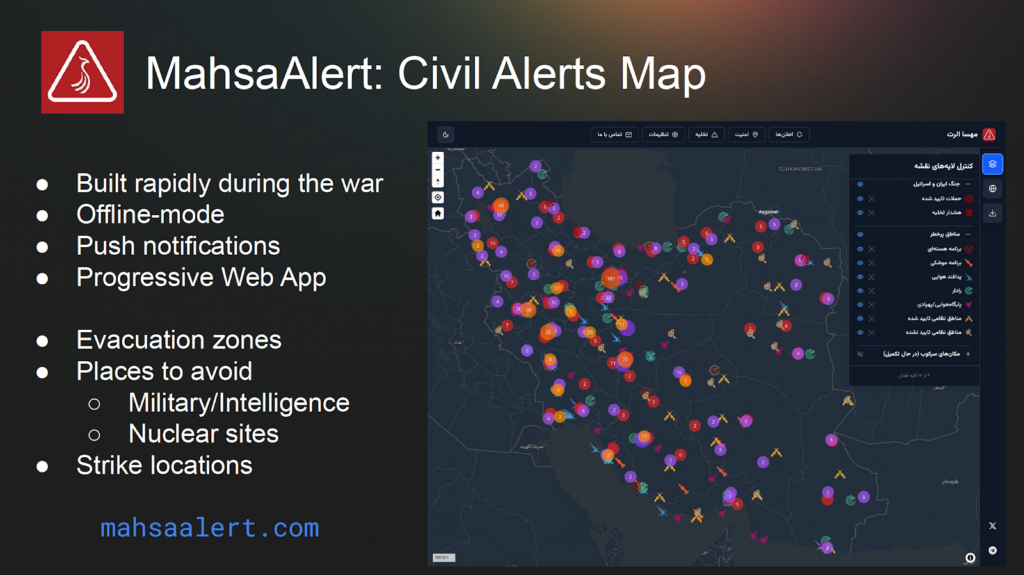
MahsaNet also extends beyond tunneling. During wartime, the team built MahsaAlert, a Progressive Web App designed to provide civil alerts with offline capability. It includes evacuation zones, strike locations, and markers for military or intelligence sites. Offline caching and PWA architecture allow partial functionality even during degraded connectivity. This represents an important shift: circumvention is not only about reaching social media but about preserving situational awareness when infrastructure collapses. In shutdown environments, the ability to disseminate or cache critical information can have direct life-saving implications.
Finally, CensorDB introduces a structured intelligence layer. This crowdsourced censorship database aggregates data, enables user submissions, and exports configurations compatible with tools like V2ray and sing-box. By transforming censorship events into analyzable datasets, MahsaNet shortens the feedback loop between detection and response. Rather than reacting blindly to blocking waves, developers can adapt configurations based on empirical filtering evidence. Over time, this creates a learning system that improves resilience against recurring techniques.
Taken together, MahsaNet’s architecture operates across multiple layers: dynamic configuration distribution, multi-protocol client agility, decentralized server deployment, embedded circumvention frameworks, wartime civil information tools, and a data-driven censorship intelligence database. This layered approach is essential in high-intensity filtering environments, where regimes combine DPI, infrastructure pressure, legal threats, and psychological operations.
For people on the ground during shutdowns, the practical implications are significant. Adaptive config distribution increases the probability of reconnecting during filtering spikes. Self-hosted infrastructure reduces dependence on politically exposed intermediaries. Offline-capable civil alert tools preserve critical information flows when connectivity is intermittent. And structured censorship data accelerates recovery after blocking events. MahsaNet thus represents more than a VPN. It is an attempt to engineer operational resilience under digital siege building an ecosystem that evolves as quickly as the censorship apparatus it confronts.
NasNet: Building Shutdown-Proof Connectivity for a Free Internet
NasNet is the largest Farsi-speaking Starlink community in the world building parallel networks that offer more independence from governmental control and shutdown resilience. Currently, over 50000 terminals are active in Iran. The project started as a technically complex inititative facing network engineers, with a hard to digest 52 pages guide. It has progressively evolved into a user-facing easy to install solution with a configuration generator based on only 8 questions. Due to the censors capacities to quickly learn about and suppress circumvention technologies, NasNet has introduced the Nas Net Panel, a dynamic connectivity stack.
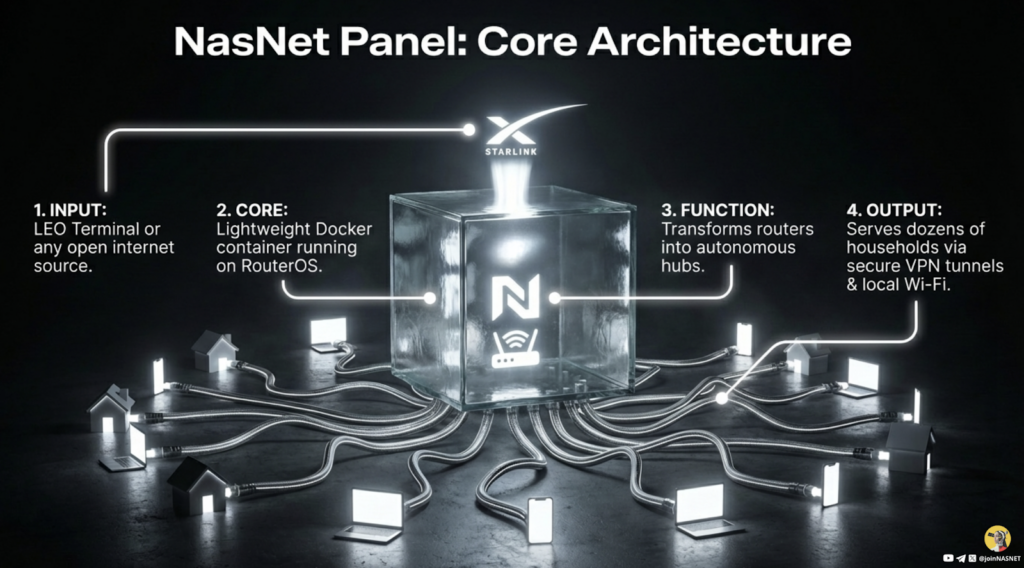
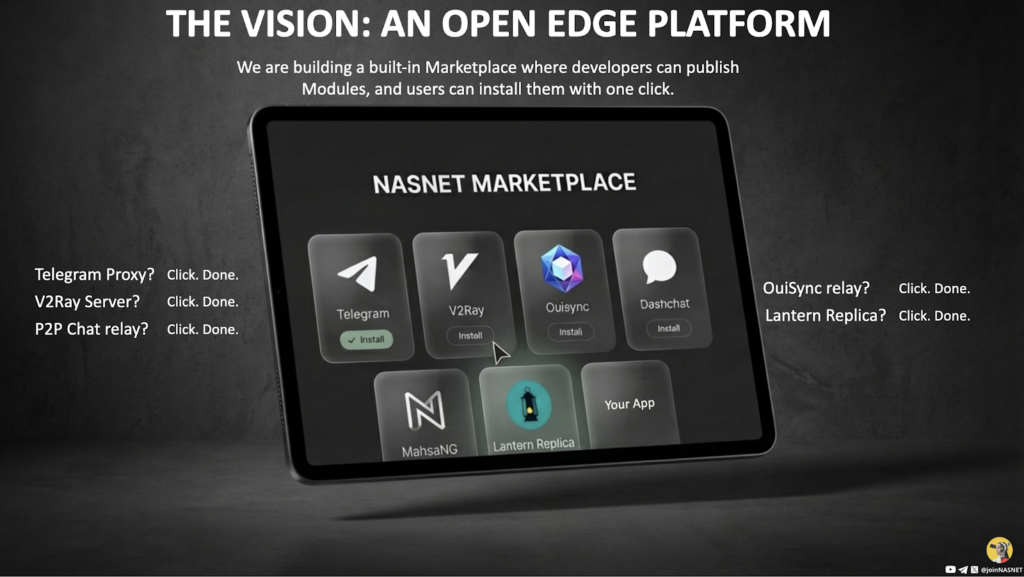
NasNet stack is source agnostic. In the future it will be used not just with Starlink but with other LEO providers such as Amazon Project Kuiper, but also with mobile connectivity technologies (SIMs, e-SIMs, Direct-to-Cell). In the future it will support any open internet source. Currently the Proof of concept has been released and the project is actively field-tested. Next steps include One-click installation, Multi-link Failover and finally releasing the Edge Platform that supports other applications.
Ouisync for websites
In splintered environments, applications and services that depend on centralized cloud infrastructure face several challenges such as synchronizing application state across devices, distributing files or content to users and providing access to up-to-date web content when origin servers are unreachable. Traditional client-server architectures fail when connectivity to central servers disappears. Ouisync can the be used as a decentralized mechanism to maintain data availability and synchronization in these constrained conditions.
Ouisync is a user facing application for secure p2p file sharing developed by eQualitie. But it is also a distributed storage and transport library with an API. It allows encrypted storage, mutable content-addressable data structures, peer-to-peer synchronization and does not depend on centralized servers. The system supports synchronization among trusted and untrusted peers, enabling distributed collaboration and content distribution. Ouisync relies on DHT (Distributed Hash Table) for peer discovery, PEX (Peer Exchange) for network topology expansion and Local discovery on LAN.
Ouisync implements three access models: Read-Write (Multiple participants can modify data) Read-Only (Users can only read content shared by the repository owner) and Blind (Repository is stored but can not be read). These modes enable different collaboration models and allow fine-grained control over distribution and collaboration scenarios.
Ouisync can synchronize application state across user devices: data stays end-to-end encrypted, no user accounts or centralized services are required, optional caching server can be added. One of the intergration use-cases is the Ceno browser where Ouisync helps to synchronize browser settings and cached content between devices using the Ceno browser app.
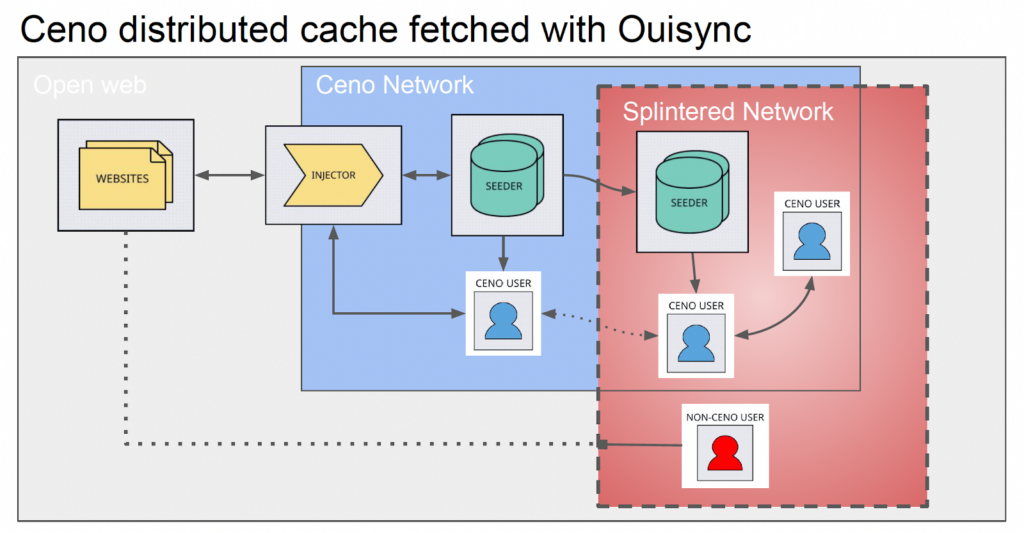
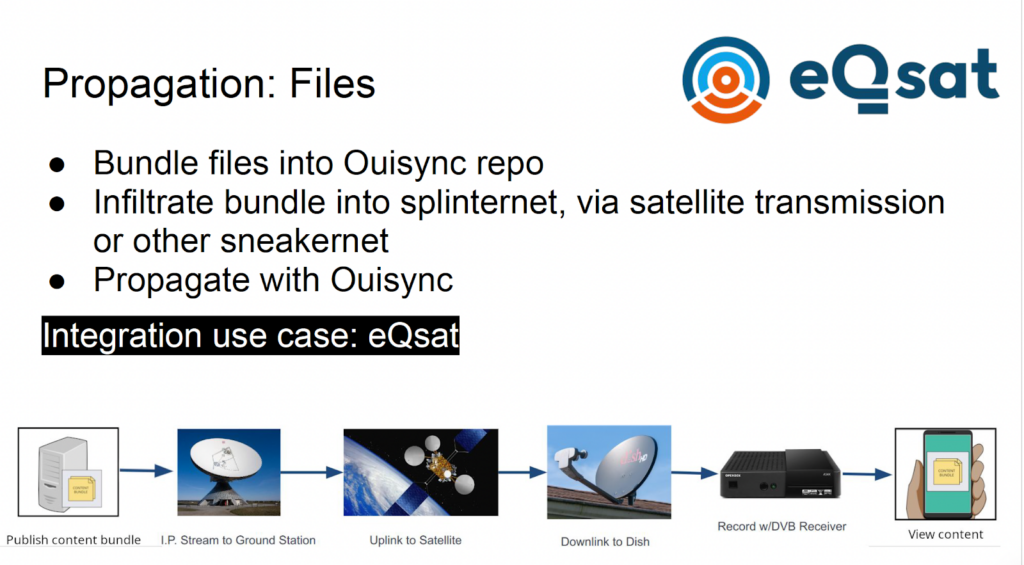
Ouisync can be used to transfer data in the case of splinternet. Files can be packaged into an Ouisync repository bundle and injected into restricted networks. Distribution methods include: satellite transmission, sneakernet (physical transport) and offline injection points. Content bundles are transmitted via satellite and propagated locally through peer-to-peer synchronization.
The integration of Ouisync with 451 tools enables automatic synchronization and propagation of website mirrors. If the 451 tools plugin is added to a website, the user can accesse a website normally and in the case of blocking, the system will redirect the user to a mirror. Ouisync keeps mirrors synchronized with the latest content.
Traditional ways of updating mirrors with fresh data (e.g. rsync, scp, sftp) have the disadvantage that if the mirror is positioned inside a censored country, access to the data source can be easily blocked. This is due to the static acyclic graph network topology implied by these tools. Ouisync instances can update themselves with new data in both directions and will automatically attempt to establish connections to other instances even if those are deployed later. This implies a dynamic network topology permitting cycles which is harder to block and simpler to maintain.
Besides mentioned use-case examples, Ouisync can be integrated in other applications through library integration, Linux CLI and Storage Access Framework. Ouisync provides a secure, decentralized data layer for applications and content distribution that works even when the global Internet is fragmented, central servers are unavailable or connectivity is intermittent. By combining encrypted repositories, peer discovery mechanisms, and flexible distribution models, Ouisync enables resilient information flows across fragmented networks.